|
TECHNICAL REPORT
CYBER;
Critical Security Controls for Effective Cyber Defence;
Part 4: Facilitation Mechanisms
---------------------- Page: 1 ----------------------
2 ETSI TR 103 305-4 V2.1.1 (2018-09)
Reference
RTR/CYBER-0034-4
Keywords
cyber security, cyber-defence, information
assurance
ETSI
650 Route des Lucioles
F-06921 Sophia Antipolis Cedex - FRANCE
Tel.: +33 4 92 94 42 00 Fax: +33 4 93 65 47 16
Siret N° 348 623 562 00017 - NAF 742 C
Association à but non lucratif enregistrée à la
Sous-Préfecture de Grasse (06) N° 7803/88
Important notice
The present document can be downloaded from:
The present document may be made available in electronic versions and/or in print. The content of any electronic and/or
print versions of the present document shall not be modified without the prior written authorization of ETSI. In case of any
existing or perceived difference in contents between such versions and/or in print, the only prevailing document is the
print of the Portable Document Format (PDF) version kept on a specific network drive within ETSI Secretariat.
Users of the present document should be aware that the document may be subject to revision or change of status.
Information on the current status of this and other ETSI documents is available at
If you find errors in the present document, please send your comment to one of the following services:
Copyright Notification
No part may be reproduced or utilized in any form or by any means, electronic or mechanical, including photocopying
and microfilm except as authorized by written permission of ETSI.
The content of the PDF version shall not be modified without the written authorization of ETSI.
The copyright and the foregoing restriction extend to reproduction in all media.
© ETSI 2018.
All rights reserved.
TM TM TM
DECT , PLUGTESTS , UMTS and the ETSI logo are trademarks of ETSI registered for the benefit of its Members.
TM TM
3GPP and LTE are trademarks of ETSI registered for the benefit of its Members and
of the 3GPP Organizational Partners.
oneM2M logo is protected for the benefit of its Members.
GSM and the GSM logo are trademarks registered and owned by the GSM Association.
ETSI
---------------------- Page: 2 ----------------------
3 ETSI TR 103 305-4 V2.1.1 (2018-09)
Contents
Intellectual Property Rights . 4
Foreword . 4
Modal verbs terminology . 4
Executive summary . 4
Introduction . 4
1 Scope . 5
2 References . 5
2.1 Normative references . 5
2.2 Informative references . 5
3 Definitions and abbreviations . 5
3.1 Definitions . 5
3.2 Abbreviations . 6
4 Hardened Images . 6
4.1 Description . 6
4.2 Virtual Image vs. Hardened Virtual Image . 6
4.3 Benefits of Hardened Images . 6
5 Mappings and Compliance . 7
5.1 Description . 7
6 Guide for Small and Medium-sized Enterprises (SMEs) . 7
6.1 Description . 7
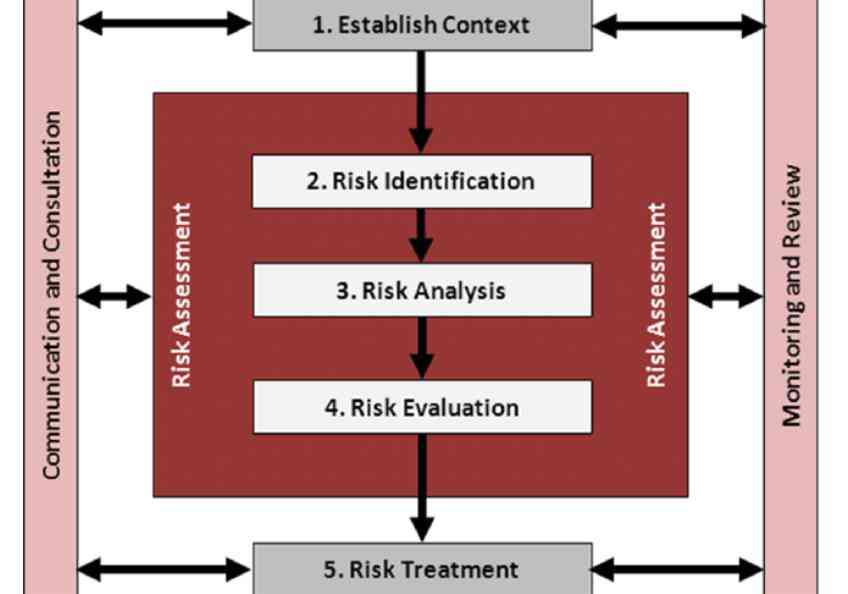
7 Risk Assessment Method (RAM) . 8
7.1 Description . 8
History . 9
ETSI
---------------------- Page: 3 ----------------------
4 ETSI TR 103 305-4 V2.1.1 (2018-09)
Intellectual Property Rights
Essential patents
IPRs essential or potentially essential to normative deliverables may have been declared to ETSI. The information
pertaining to these essential IPRs, if any, is publicly available for ETSI members and non-members, and can be found
in ETSI SR 000 314: "Intellectual Property Rights (IPRs); Essential, or potentially Essential, IPRs notified to ETSI in
respect of ETSI standards", which is available from the ETSI Secretariat. Latest updates are available on the ETSI Web
server (https://ipr.etsi.org/).
Pursuant to the ETSI IPR Policy, no investigation, including IPR searches, has been carried out by ETSI. No guarantee
can be given as to the existence of other IPRs not referenced in ETSI SR 000 314 (or the updates on the ETSI Web
server) which are, or may be, or may become, essential to the present document.
Trademarks
The present document may include trademarks and/or tradenames which are asserted and/or registered by their owners.
ETSI claims no ownership of these except for any which are indicated as being the property of ETSI, and conveys no
right to use or reproduce any trademark and/or tradename. Mention of those trademarks in the present document does
not constitute an endorsement by ETSI of products, services or organizations associated with those trademarks.
Foreword
This Technical Report (TR) has been produced by ETSI Technical Committee Cyber Security (CYBER).
The present document is part 4 of a multi-part deliverable covering the Critical Security Controls for Effective Cyber
Defence. Full details of the entire series can be found in part 1 [i.1].
Modal verbs terminology
In the present document "should", "should not", "may", "need not", "will", "will not", "can" and "cannot" are to be
interpreted as described in clause 3.2 of the ETSI Drafting Rules (Verbal forms for the expression of provisions).
"must" and "must not" are NOT allowed in ETSI deliverables except when used in direct citation.
Executive summary
The Critical Security Controls represent perhaps the most valuable cyber defence mechanism worldwide and across
multiple ICT sectors because of the many facilitation mechanisms which have been developed to assist with their
implementation and use. The present document is an evolving repository for some of the most important facilitation
mechanism for Critical Security Control.
Introduction
The Critical Security Controls ("the Controls") exist within a larger cyber security ecosystem that relies on the Controls
as critically important defensive measures. There are a variety of facilitation mechanisms for their use. The present
document provides a placeholder for reference information for several especially useful mechanisms: Hardened Images,
Mappings and Compliance, Guide for Small- and Medium-Sized Enterprises, and Risk Assessment Method.
ETSI
---------------------- Page: 4 ----------------------
5 ETSI TR 103 305-4 V2.1.1 (2018-09)
1 Scope
The present document is an evolving repository for diverse facilitation mechanism guidelines for Critical Security
Control implementations.
2 References
2.1 Normative references
Normative references are not applicable in the present document.
2.2 Informative references
References are either specific (identified
...